

Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a server named Server1 that runs Windows Server.
You need to ensure that only specific applications can modify the data in protected folders on Server1.
Solution: From Virus & threat protection, you configure Controlled folder access.
Does this meet the goal?
Correct Answer:
A
🗳️
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a server named Server1 that runs Windows Server.
You need to ensure that only specific applications can modify the data in protected folders on Server1.
Solution: From Virus & threat protection, you configure Tamper Protection
Does this meet the goal?
Correct Answer:
B
🗳️
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a server named Server1 that runs Windows Server.
You need to ensure that only specific applications can modify the data in protected folders on Server1.
Solution: From App & browser control, you configure the Exploit protection settings.
Does this meet the goal?
Correct Answer:
B
🗳️
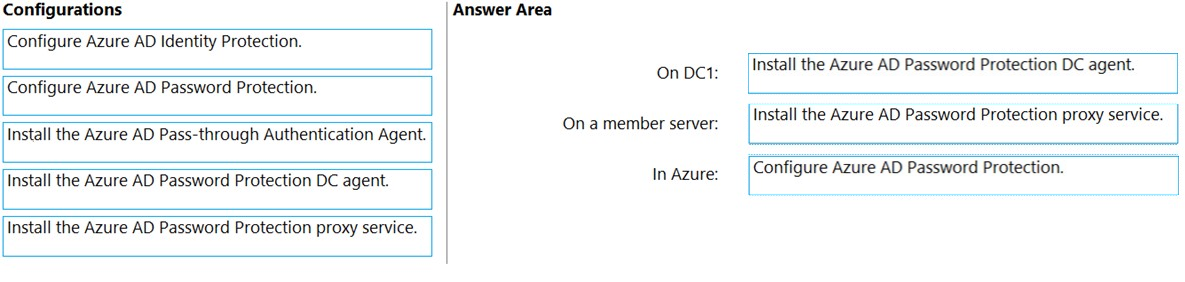
DRAG DROP -
You have an on-premises Active Directory Domain Services (AD DS) domain that syncs with an Azure Active Directory (Azure AD) tenant.
The AD DS domain contains a domain controller named DC1. DC1 does NOT have internet access.
You need to configure password security for on-premises users. The solution must meet the following requirements:
✑ Prevent the users from using known weak passwords.
✑ Prevent the users from using the company name in passwords.
What should you do? To answer, drag the appropriate configurations to the correct targets. Each configuration may be used once, more than once, or not at all.
You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
Select and Place: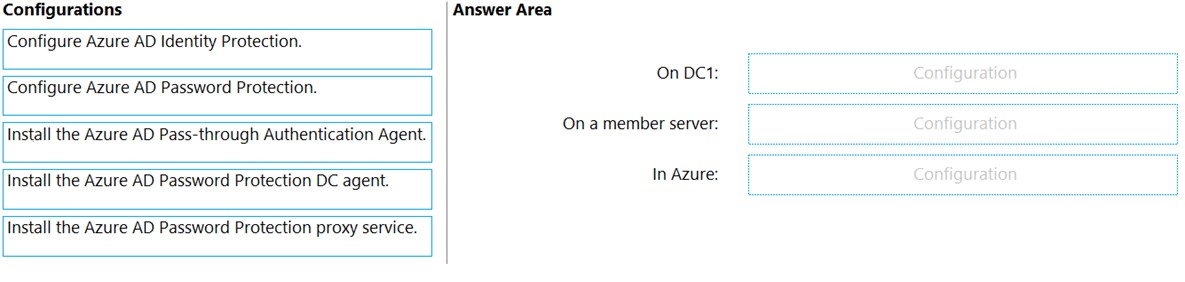
Correct Answer:
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/authentication/howto-password-ban-bad-on-premises-deploy
HOTSPOT -
The Default Domain Policy Group Policy Object (GPO) is shown in the GPO exhibit. (Click the GPO tab.)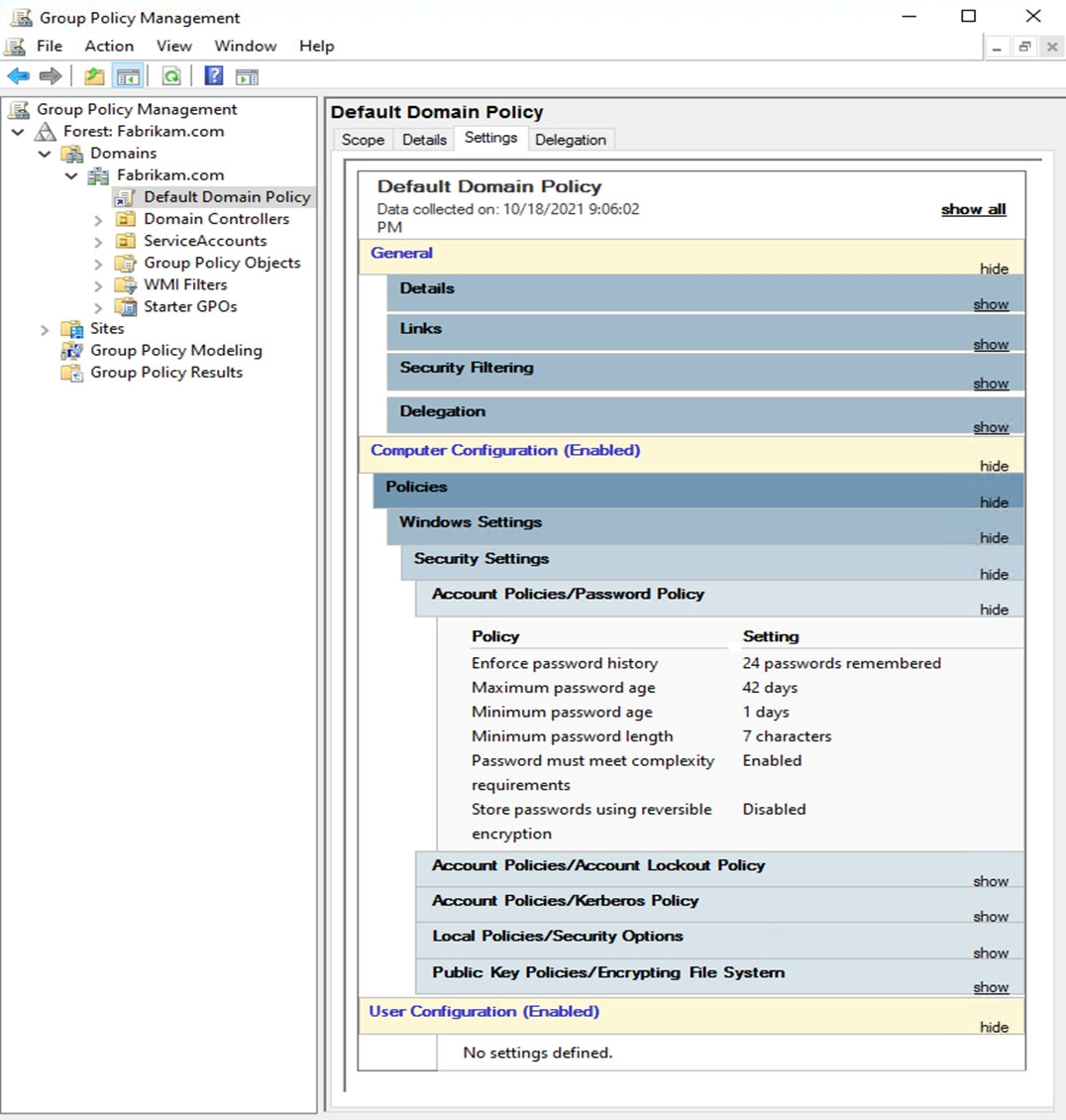
The members of a group named Service Accounts are shown in the Group exhibit. (Click the Group tab.)
An organizational unit (OU) named ServiceAccounts is shown in the OU exhibit. (Click the OU tab.)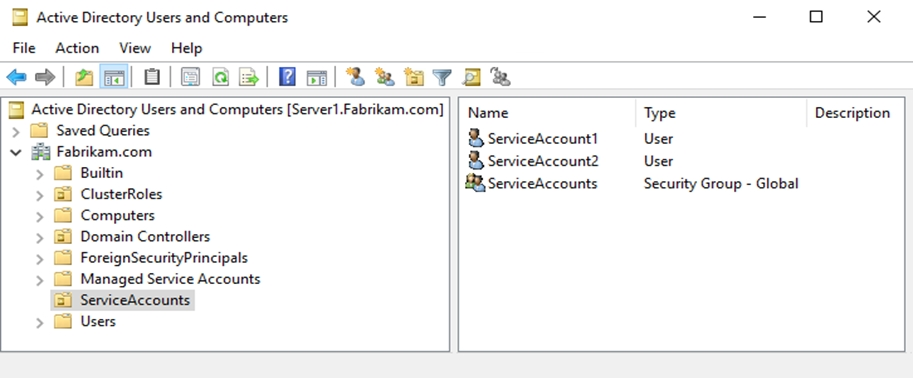
You create a Password Settings Object (PSO) as shown in the PSO exhibit. (Click the PSO tab.)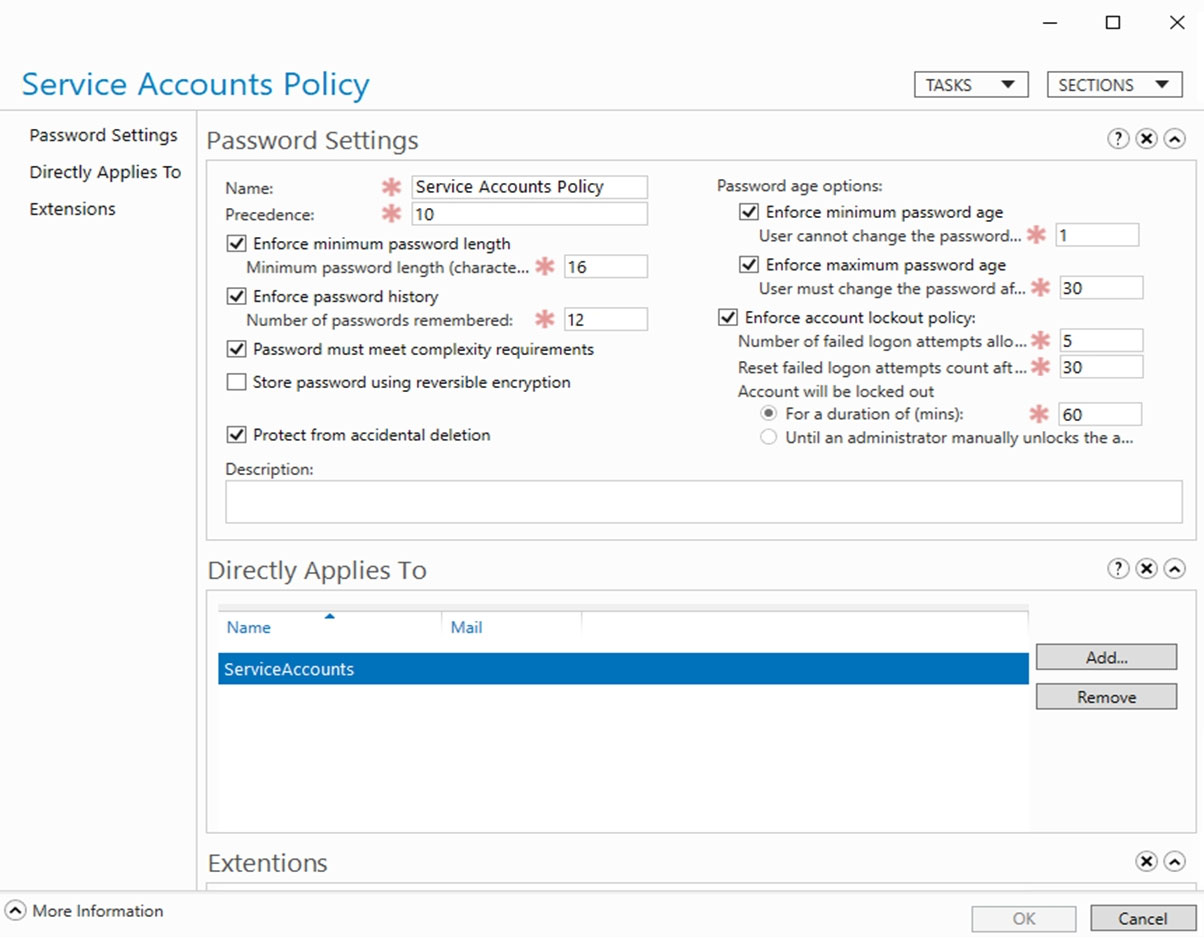
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Hot Area: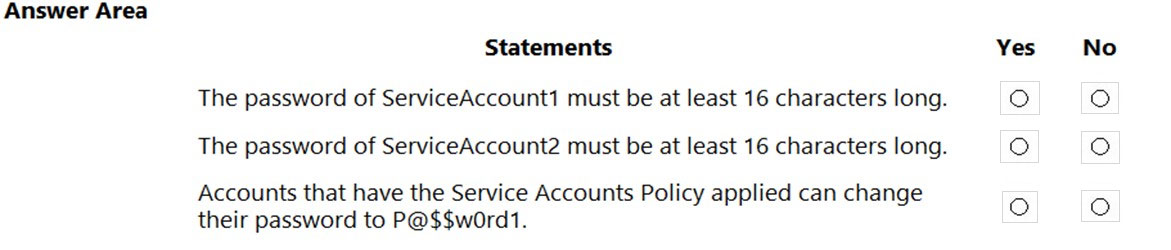
Correct Answer:
Reference:
https://docs.microsoft.com/en-us/windows-server/identity/ad-ds/get-started/adac/introduction-to-active-directory-administrative-center-enhancements--level-100-
#fine_grained_pswd_policy_mgmt
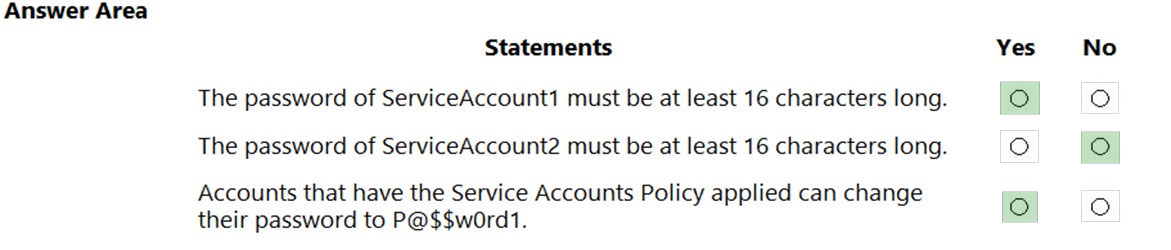
DRAG DROP -
Your network contains an Active Directory Domain Services (AD DS) domain.
You need to implement a solution that meets the following requirements:
✑ Ensures that the members of the Domain Admins group are allowed to sign in only to domain controllers
✑ Ensures that the lifetime of Kerberos Ticket Granting Ticket (TGT) for the members of the Domain Admins group is limited to one hour
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
Select and Place: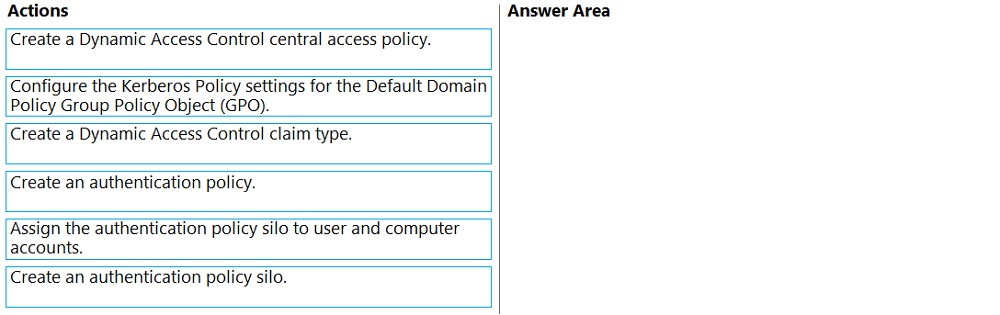
Correct Answer:
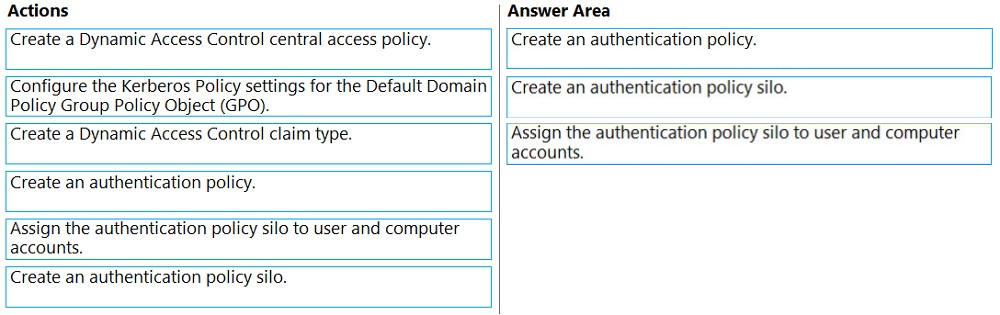
Reference:
https://docs.microsoft.com/en-us/windows-server/identity/ad-ds/manage/how-to-configure-protected-accounts
You have an Azure virtual machine named VM1 that runs Windows Server.
You plan to deploy a new line-of-business (LOB) application to VM1.
You need to ensure that the application can create child processes.
What should you configure on VM1?
Correct Answer:
D
🗳️
HOTSPOT -
Your network contains an Active Directory Domain Services (AD DS) domain named contoso.com. The domain contains the organizational units (OUs) shown in the following table.
In the domain, you create the Group Policy Objects (GPOs) shown in the following table.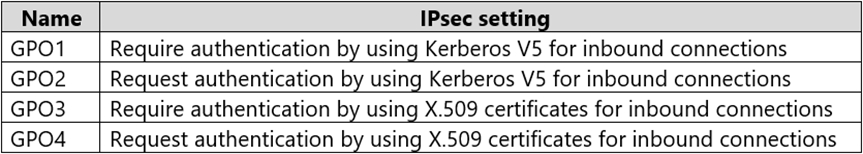
You need to implement IPsec authentication to ensure that only authenticated computer accounts can connect to the members in the domain. The solution must minimize administrative effort.
Which GPOs should you apply to the Domain Controllers OU and the Domain Servers OU? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area: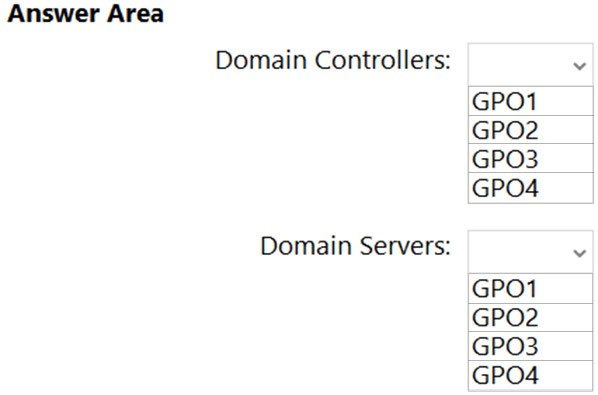
Correct Answer:
Reference:
https://docs.microsoft.com/en-us/windows/security/threat-protection/windows-firewall/configure-authentication-methods
You have 100 Azure virtual machines that run Windows Server. The virtual machines are onboarded to Microsoft Defender for Cloud.
You need to shut down a virtual machine automatically if Microsoft Defender for Cloud generates the "Antimalware disabled in the virtual machine" alert for the virtual machine.
What should you use in Microsoft Defender for Cloud?
Correct Answer:
A
🗳️
You have a Microsoft Sentinel deployment and 100 Azure Arc-enabled on-premises servers. All the Azure Arc-enabled resources are in the same resource group.
You need to onboard the servers to Microsoft Sentinel. The solution must minimize administrative effort.
What should you use to onboard the servers to Microsoft Sentinel?
Correct Answer:
B
🗳️